With this post, I will be stepping through a “crackme,” or a program developed for the sole purpose of bypassing software security mechanisms. A number of tools will be used for this walkthrough, including a debugger and a hex editor. The specific tool I will be using is Ollydbg for my debugger. This tool is for the Windows platform and is free to download.
The crackme that I will be walking through is called FAKE.exe. If you’re following along, download FAKE.exe along with Ollydbg.
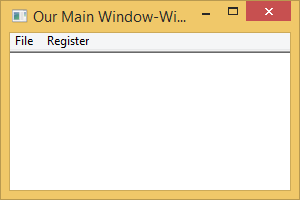
First, I will execute FAKE.exe to see what the program looks like and what it does:
Not very interesting, but clicking on the “Register” menu item reveals a registration dialog:

I typed “123456789” into the box and clicked “Enter Serial” and was presented with the following:
 Let’s open up Ollydbg, and use it to see if we can make “123456789” a correct serial number!
Let’s open up Ollydbg, and use it to see if we can make “123456789” a correct serial number!
In Ollydbg, go to File->Open and select FAKE.exe. The file will load and you will see a window like the following:
In order to find where the program checks the serial number, we will search for the referenced strings used by the program. Essentially, the phrase “That serial is incorrect” should be close to the program check to determine if the serial number is correct or not. To search for the referenced strings in Ollydbg, right-click the main section and go through the “Search for->All reference strings” contextual menu.
A new window will appear with the referenced strings. We are searching for the “That serial is incorrect” string.
 We can see that this string is easily found in this small executable program. Double-click that string to get close to the checking portion of the program. When double-clicking this string, we can also see that the “That serial is correct!!!!!” string is very close. How can we manipulate the program flow to see this message?
We can see that this string is easily found in this small executable program. Double-click that string to get close to the checking portion of the program. When double-clicking this string, we can also see that the “That serial is correct!!!!!” string is very close. How can we manipulate the program flow to see this message?
If we follow the small arrows next to the low-level instructions, we can see that the arrow originates at a JNE instruction, as highlighted in green below:
The JNE instructions stands for “Jump if not equal.” It is used in conjuction with the CMP instruction right before it. CMP compares two values and sets the zero flag register if they are equal. JNE looks at the zero flag and if it is not set, then the jump is taken. Otherwise the jump is ignored and goes to the next instruction.
Since the JNE instruction goes to the “That serial is incorrect” string (or near it rather), we do not want this jump to happen. So double click the three CMP instructions to set break points (the address of the instruction will turn red) and execute the program by clicking the “play” icon in the toolbar.
The program will run. Click the “Register” menu item and type in “123456789” into the serial number box and click “Enter Serial.” The program will pause execution at that CMP instruction. Pay attention to the CPU registers on the right hand side, in particular the Z flag. This is the zero flag register.
 Click on the Debug->Step Over menu item to advance one CPU instruction. You will notice that the arrow next to the JNE instruction will be red. This means the jump will be taken. Double-click the Z flag on the right to change that 0 to a 1. The arrow will turn black.
Click on the Debug->Step Over menu item to advance one CPU instruction. You will notice that the arrow next to the JNE instruction will be red. This means the jump will be taken. Double-click the Z flag on the right to change that 0 to a 1. The arrow will turn black.
 Click the “play” icon again to resume execution. The program will pause at the next CMP instruction. Step over the CMP instruction to the JNE instruction and change the Z flag to 1 just like before. Repeat for the third break point set. When you click the play icon for the third time, you will see this in the registration dialog:
Click the “play” icon again to resume execution. The program will pause at the next CMP instruction. Step over the CMP instruction to the JNE instruction and change the Z flag to 1 just like before. Repeat for the third break point set. When you click the play icon for the third time, you will see this in the registration dialog:
You win!
Keep in mind that this is an incredibly simple registration dialog. Actual programs are much more difficult. Enjoy this peek into what reverse code engineering is like! If you’re interested in learning more about Ollydbg, you can watch the following video:











